Understanding the perpetual free offerings of major cloud providers
The cloud computing landscape is dominated by a few key players, each offering a range of services to cater to diverse needs. Among these giants, Microsoft Azure, Google Cloud Platform (GCP), Amazon Web Services (AWS), and Oracle Cloud Infrastructure (OCI) stand out. One of the most compelling reasons for individuals and businesses to explore these platforms is the availability of free forever tiers. These free tiers provide an opportunity to experiment, develop, and even deploy applications without incurring significant costs. In this blog, we will delve into and compare the free forever tier offerings of Azure, GCP, AWS, and OCI.
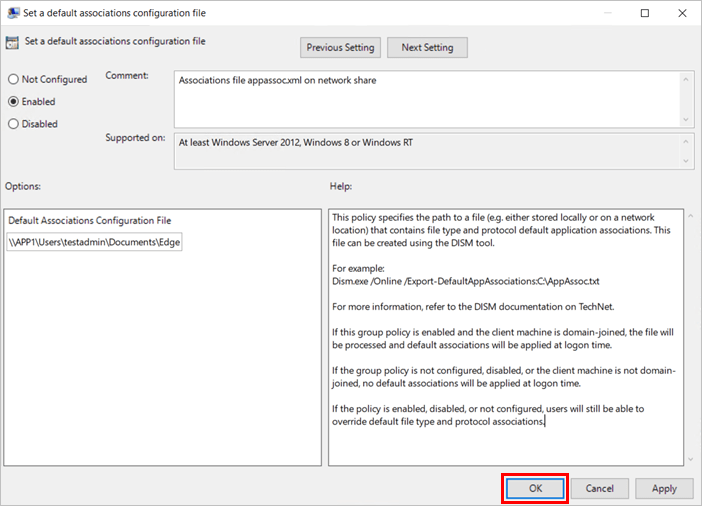
Microsoft Azure
Microsoft Azure offers several services that remain free forever. These always free services include:
- Azure Functions: 1 million requests per month
- File Storage: 5 GB of LRS (Locally Redundant Storage)
- SQL Database: 250 GB of storage
Google Cloud Platform (GCP)
Google Cloud Platform provides a variety of services that are always free, which include:
- Compute Engine: 1 f1-micro instance per month in select regions
- Cloud Storage: 5 GB of Regional Storage
- Network Egress: 1 GB from North America to all regions
Amazon Web Services (AWS)
Amazon Web Services offers an extensive array of services that are perpetually free. These always free services include:
- AWS Lambda: 1 million requests per month
- DynamoDB: 1 GB of storage
- Glacier: 25 GB of data retrievals
Oracle Cloud Infrastructure (OCI)
Oracle Cloud Infrastructure provides several services that are free forever, including:
- Autonomous Database: 2 instances with Oracle APEX
- Compute VMs: 2 AMD-based virtual machines
- Data Transfer: 10 TB outbound per month
Comparison and Conclusion
When comparing the free forever tiers of Azure, GCP, AWS, and OCI, several key points stand out:
- Service variety: Each provider offers a range of services under their always free tier, from computing instances to storage and databases. AWS tends to have one of the most extensive always free offerings, while OCI provides substantial data transfer and compute options.
- Use case suitability: Depending on your needs—whether it’s running virtual machines, exploring database options, or experimenting with cloud functions—you might find one provider’s free tier more suitable than the others. For instance, AWS is excellent for those needing a broad range of services, while OCI provides substantial data transfer and compute options.
In conclusion, the choice of a cloud provider’s free forever tier should align with your specific requirements and future scalability plans. Each provider—Azure, GCP, AWS, and OCI—brings unique strengths to the table, making it essential to analyze which free tier best fits your project needs.
Whether you’re a developer, a small business, or a large enterprise, leveraging these free forever tiers can provide a cost-effective way to innovate and grow in the cloud.
The final verdict with a lead of 2 free VMs for life on its free forever tier, OCI takes the crown.